- Jenkins Pipeline Cheat Sheet
- Jenkins Pipeline Pdf
- Jenkins Cheat Sheet Pdf
- Jenkins Manual
- Jenkins Command Cheat Sheet
- Jenkins Cheat Sheet Pdf
Updated March 26th, 2021
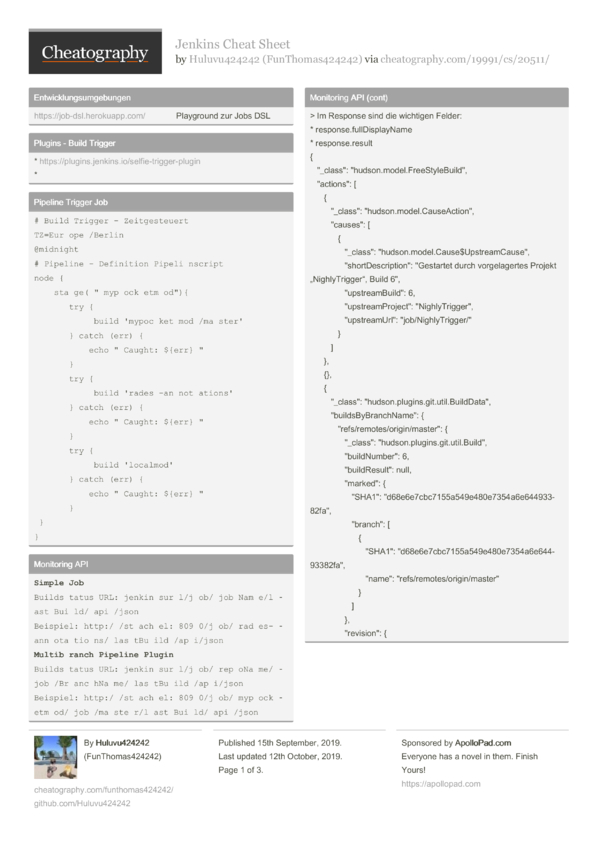
Jenkins Pipeline DSL Cheat Sheet Edit Cheat Sheet Using Kubernetes. When running jobs as Kubernetes pods you need to specify/inherit podTemplates. From local Jenkins. For this to work you have to configure a global or per-folder shared library which you can. Big O Cheat Sheet 7 Time Complexity Classes on 1 Page Use this 1-page PDF cheat sheet as a reference to quickly look up the seven most important time complexity classes (with descriptions and examples). Groovy/Scripted cheat sheet? Posted by 1 day ago. I set up Jenkins in docker and a few additional containers which have our build environment set up and a few machines that can handle all of our build needs. I then built a declarative pipeline which can (with a change in parameters) build any of the streams that I point it at.
Pipeline Steps Reference List of Pipeline-compatible steps provided by the various Jenkins plugins, offering information about the parameters for each step. About Just another cheat sheet of Jenkins pipeline script snippets.
This blog post has been updated based on some tools and techniques from Offensive Security’s PEN-300 course (for the accompanying OSEP certification). Notable changes have been made in the sections on delegation, inter-forest exploitation, and lateral movement through MSSQL servers. Some other changes and clarifications have been made throughout the post.
Since I recently completed my CRTP and CRTE exams, I decided to compile a list of my most-used techniques and commands for Microsoft Windows and Active Directory (post-)exploitation. It is largely aimed at completing these two certifications, but should be useful in a lot of cases when dealing with Windows / AD exploitation.
That being said - it is far from an exhaustive list. If you feel any important tips, tricks, commands or techniques are missing from this list just get in touch. I will try to keep it updated as much as possible!
Many items of this list are shamelessly stolen from Nikhil Mittal and the CRTP/CRTE curricula, so big thanks to them!If you are looking for the cheat sheet and command reference I used for OSCP, please refer to this post.
Note: I tried to highlight some poor OpSec choices for typical red teaming engagements with 🚩. I will likely have missed some though, so, understand what you are running before you run it!
General
PowerShell AMSI Bypass
Patching AMSI will help bypass AV warnings triggered when executing PowerShell scripts that are marked as malicious (such as PowerView). Do not use as-is in covert operations, as they will get flagged 🚩. Obfuscate, or even better, eliminate the need for an AMSI bypass altogether by altering your scripts to beat signature-based detection.
‘Plain’ AMSI bypass:
Obfuscation example for copy-paste purposes:
Another bypass, which is not detected by PowerShell autologging:
More bypasses here. For obfuscation, check Invoke-Obfuscation, or get a pre-generated obfuscated version at amsi.fail.
PowerShell one-liners
Load PowerShell script reflectively
Proxy-aware:
Non-proxy aware:
Jenkins Pipeline Cheat Sheet
Again, this will likely get flagged 🚩. For opsec-safe download cradles, check out Invoke-CradleCrafter.
Load C# assembly reflectively
Ensure that the referenced class and main methods are Public before running this. Note that a process-wide AMSI bypass may be required for this, refer here for details.
Download file
Encode command
Encode one-liner:
Or, the Linux version of the above:
Encode existing script, copy to clipboard:
Run it, bypassing execution policy.
If you have Nishang handy, you can use Invoke-Encode.ps1.
Enumeration
AD Enumeration With PowerView
AppLocker
Identify AppLocker policy. Look for exempted binaries or paths to bypass.
Some high-level bypass techniques:
- Use LOLBAS if only (Microsoft-)signed binaries are allowed.
- If binaries from
C:Windowsare allowed, try dropping your binaries toC:WindowsTemporC:WindowsTasks. If there are no writable subdirectories but writable files exist in this directory tree, write your file to an alternate data stream (e.g. a JScript script) and execute it from there. - Wrap your binaries in a DLL file and execute them with
rundll32to bypass executable rules. If binaries like Python are allowed, use that. If that doesn’t work, try other techniques such as wrapping JScript in a HTA file or running XSL files withwmic.
PowerShell Constrained Language Mode
Sometimes you may find yourself in a PowerShell session that enforces Constrained Language Mode (CLM). This is very often the case when paired with AppLocker (see above).
You can identify you’re in constrained language mode by polling the following variable to get the current language mode. It will say FullLanguage for an unrestricted session, and ConstrainedLanguage for CLM. There are other language modes which I will not go into here.
The constraints posed by CLM will block many of your exploitations attempts. One quick and dirty bypass is to use in-line functions, which sometimes works - if e.g. whoami is blocked, try the following:
LAPS
We can use LAPSToolkit.ps1 to identify which machines in the domain use LAPS, and which domain groups are allowed to read LAPS passwords. If we are in this group, we can get the current LAPS passwords using this tool as well.
Exploitation
Powercat reverse shell
If a reverse shell to your Linux box is not an option ;).
Lateral Movement
Lateral Movement Enumeration With PowerView
BloodHound
Use Invoke-BloodHound from SharpHound.ps1, or use SharpHound.exe. Both can be ran reflectively, get them here.
Kerberoasting
Automatic
With PowerView:
Crack the hash with Hashcat:
Manual
Targeted kerberoasting by setting SPN
We need ACL write permissions to set UserAccountControl flags for said user, see above for hunting. Using PowerView:
AS-REP roasting
Get the hash for a roastable user (see above for hunting). Using ASREPRoast.ps1:
Crack the hash with Hashcat:
Targeted AS-REP roasting by disabling Kerberos pre-authentication
We need ACL write permissions to set UserAccountControl flags for said user, see above for hunting. Uses PowerView.
Token Manipulation
Tokens can be impersonated from other users with a session/running processes on the machine. A similar effect can be achieved by using e.g. CobaltStrike to inject into said processes.
Incognito
If you’re using Meterpreter, you can use the built-in Incognito module with use incognito, the same commands are available.
Invoke-TokenManipulation
Mimikatz
A list of available SPNs for silver tickets can be found here. Another nice overview for SPNs relevant for offensive is provided here.
Command execution with schtasks
Requires ‘Host’ SPN
Jenkins Pipeline Pdf
To create a task:
To trigger it:
Command execution with WMI
Requires ‘Host’ and ‘RPCSS’ SPNs
From Windows
From Linux
Command execution with PowerShell Remoting
Requires ‘CIFS’, ‘HTTP’ and ‘WSMAN’ SPNs
This one is a bit tricky. A combination of the above SPNs may or may not work - also PowerShell may require the exact FQDN to be provided.
Unconstrained delegation
Can be set on a frontend service (e.g., IIS web server) to allow it to delegate on behalf of the user to any service in the domain (towards a backend service, such as an MSSQL database).
DACL UAC property: TrustedForDelegation.
Exploitation
With administrative privileges on a server with Unconstrained Delegation set, we can dump the TGTs for other users that have a connection. With Mimikatz:
Or with Rubeus:
We can also gain the hash for a domain controller machine account, if that DC is vulnerable to the printer bug. On the server with Unconstrained Delegation, monitor for new tickets with Rubeus.
From attacking machine, entice the Domain Controller to connect using the printer bug. Binary from here.

The TGT for the machine account of the DC should come in in the first session. We can pass this ticket to gain DCSync privileges.
Constrained delegation
Constrained delegation can be set on the frontend server (e.g. IIS) to allow it to delegate to only selected backend services (e.g. MSSQL) on behalf of the user.
DACL UAC property: TrustedToAuthForDelegation. This allows s4u2self, i.e. requesting a TGS on behalf of anyone to oneself, using just the NTLM password hash. This effectively allows the service to impersonate other users in the domain with just their hash, and is useful in situations where Kerberos isn’t used between the user and frontend.
DACL Property: msDS-AllowedToDelegateTo. This property contains the SPNs it is allowed to use s4u2proxy on, i.e. requesting a forwardable TGS for that server based on an existing TGS (e.g. the one gained from using s4u2self). This effectively defines the backend services that constrained delegation is allowed for.
NOTE: These properties do NOT have to exist together! If s4u2proxy is allowed without s4u2self, user interaction is required to get a valid TGS to the frontend service from a user, similar to unconstrained delegation.
Exploitation
In this case, we use Rubeus to automatically request a TGT and then a TGS with the ldap SPN to allow us to DCSync using a machine account.
Resource-based constrained delegation
Resource-Based Constrained Delegation (RBCD) configures the backend server (e.g. MSSQL) to allow only selected frontend services (e.g. IIS) to delegate on behalf of the user. This makes it easier for specific server administrators to configure delegation, without requiring domain admin privileges.
DACL Property: msDS-AllowedToActOnBehalfOfOtherIdentity.
In this scenario, s4u2self and s4u2proxy are used as above to request a forwardable ticket on behalf of the user. However, with RBCD, the KDC checks if the SPN for the requesting service (i.e., the frontend service) is present in the msDS-AllowedToActOnBehalfOfOtherIdentity property of the backend service. This means that the frontend service needs to have an SPN set. Thus, attacks against RBC have to be performed from either a service account with SPN or a machine account.
Exploitation
If we compromise a frontend service that appears in the RBCD property of a backend service, exploitation is the same as with constrained delegation above. This is however not too common.
A more often-seen attack to RBCD is when we have GenericWrite, GenericAll, WriteProperty, or WriteDACL permissions to a computer object in the domain. This means we can write the msDS-AllowedToActOnBehalfOfOtherIdentity property on this machine account to add a controlled SPN or machine account to be trusted for delegation. We can even create a new machine account and add it. This allows us to compromise the target machine in the context of any user, as with constrained delegation above.
Abusing domain trust
Must be run with DA privileges.
Using domain trust key
From the DC, dump the hash of the currentdomaintargetdomain$ trust account using Mimikatz (e.g. with LSADump or DCSync). Then, using this trust key and the domain SIDs, forge an inter-realm TGT using Mimikatz, adding the SID for the target domain’s enterprise admins group to our ‘SID history’.
Pass with Rubeus.
Make sure you have the right version of Rubeus. For some reason, some of my compiled binaries were giving the error KDC_ERR_WRONG_REALM, while the CRTP-provided version worked without issue.
We can now DCSync the target domain (see below).
Using krbtgt hash
From the DC, dump the krbtgt hash using e.g. DCSync or LSADump. Then, using this hash, forge an inter-realm TGT using Mimikatz, as with the previous method.
Use a SID History (/sids) of *-516 and S-1-5-9 to disguise as the Domain Controllers group and Enterprise Domain Controllers respectively, to be less noisy in the logs.
If you are having issues creating this ticket, try adding the ‘target’ flag, e.g. /target:moneycorp.local.
Alternatively, generate a domain admin ticket with SID history of EA group.
We can now immediately DCSync the target domain, or get a reverse shell using e.g. scheduled tasks.
Abusing inter-forest trust
Since a forest is a security boundary, we can only access domain services that have been shared with the domain we have compromised (our source domain). Use e.g. BloodHound to look for users that have an account (with the same username) in both forests and try password re-use. Additionally, we can use PowerView to hunt for foreign group memberships between forests.

In some cases, it is possible that SID filtering (the protection causing the above), is disabled between forests. If you run Get-DomainTrust and you see the TREAT_AS_EXTERNAL property, this is the case! In this case, you can abuse the forest trust like a domain trust, as described above. Note that you still can NOT forge a ticket for any SID between 500 and 1000 though, so you can’t become DA (not even indirectly through group inheritance). In this case, look for groups that grant e.g. local admin on the domain controller or similar non-domain privileges. For more information, refer to this blog post.
To impersonate a user from our source domain to access services in a foreign domain, we can do the following. Extract inter-forest trust key as in ‘Using domain trust key’ above.
Use Mimikatz to generate a TGT for the target domain using the trust key:
Then, use Rubeus to ask a TGS for e.g. the CIFS service on the target DC using this TGT.
Now we can use the CIFS service on the target forest’s DC as the DA of our source domain (again, as long as this trust was configured to exist).
Abusing MSSQL databases for lateral movement
MSSQL databases can be linked, such that if you compromise one you can execute queries (or even commands!) on others in the context of a specific user (sa maybe? 😙). This can even work across forests! If we have SQL execution, we can use the following commands to enumerate database links.
We can also use PowerUpSQL to look for databases within the domain, and gather further information on (reachable) databases. We can also automatically look for, and execute queries or commands on, linked databases (even through multiple layers of database links).
If you have low-privileged access to a MSSQL database and no links are present, you could potentially force NTLM authentication by using the xp_dirtree stored procedure to access this share. If this is successful, the NetNTLM for the SQL service account can be collected and potentially cracked or relayed to compromise machines as that service account.
Example command to relay the hash to authenticate as local admin (if the service account has these privileges) and run calc.exe. Leave out the -c parameter to attempt a secretsdump instead.
Privilege Escalation
For more things to look for (both Windows and Linux), refer to my OSCP cheat sheet and command reference.
PowerUp
UAC Bypass
Using SharpBypassUAC.
In some cases, you may get away better with running a manual UAC bypass, such as the FODHelper bypass which is quite simple to execute in PowerShell.
Persistence
Startup folder
Just drop a binary. Classic 😎🚩
In current user folder, will trigger when current user signs in:
Or in the startup folder, requires administrative privileges but will trigger as SYSTEM on boot and when any user signs on:
Domain Persistence
Must be run with DA privileges.
Mimikatz skeleton key attack
Run from DC. Enables password “mimikatz” for all users 🚩.

Grant specific user DCSync rights with PowerView
Gives a user of your choosing the rights to DCSync at any time. May evade detection in some setups.
Domain Controller DSRM admin
The DSRM admin is the local administrator account of the DC. Remote logon needs to be enabled first.
Now we can login remotely using the local admin hash dumped on the DC before (with lsadump::sam, see ‘Dumping secrets with Mimikatz’ below). Use e.g. ‘overpass the hash’ to get a session (see ‘Mimikatz’ above).
Modifying security descriptors for remote WMI access
Give user WMI access to a machine, using Set-RemoteWMI.ps1 cmdlet. Can be run to persist access to e.g. DCs.
For execution, see ‘Command execution with WMI’ above.
Modifying security descriptors for PowerShell Remoting access
Give user PowerShell Remoting access to a machine, using Set-RemotePSRemoting.ps1 cmdlet. Can be run to persist access to e.g. DCs.
Jenkins Cheat Sheet Pdf
For execution, see ‘Command execution with PowerShell Remoting’ above.
Modifying DC registry security descriptors for remote hash retrieval using DAMP
Using DAMP toolkit, we can backdoor the DC registry to give us access on the SAM, SYSTEM, and SECURITY registry hives. This allows us to remotely dump DC secrets (hashes).
We add the backdoor using the Add-RemoteRegBackdoor.ps1 cmdlet from DAMP.
Dump secrets remotely using the RemoteHashRetrieval.ps1 cmdlet from DAMP (run as ‘Trustee’ user).
DCShadow
DCShadow is an attack that masks certain actions by temporarily imitating a Domain Controller. If you have Domain Admin or Enterprise Admin privileges in a root domain, it can be used for forest-level persistence.
Optionally, as Domain Admin, give a chosen user the privileges required for the DCShadow attack (uses Set-DCShadowPermissions.ps1 cmdlet).
Then, from any machine, use Mimikatz to stage the DCShadow attack.
Finally, from either a DA session OR a session as the user provided with the DCShadowPermissions before, run the DCShadow attack. Actions staged previously will be performed without leaving logs 😈
Post-Exploitation
LSASS protection
Sometimes, LSASS is configured to run as a protected process (PPL). You can query this with PowerShell as follows.
If this is the case, you can’t just dump or parse LSASS, and you need to disable the protection with something like mimidrv.sys. I won’t discuss how to do that here.
Dumping secrets with Mimikatz
Windows Credential Vault dumping
I’ve had some issues using this with Invoke-Mimikatz.ps1. Try with native Mimikatz if having issues.
Dumping secrets without Mimikatz
We can also parse system secrets without using Mimikatz on the target system directly.
Dumping LSASS
The preferred way to run Mimikatz is to do it locally with a dumped copy of LSASS memory from the target. Dumpert, Procdump, or other (custom) tooling can be used to dump LSASS memory.
After downloading the memory dump file on our attacking system, we can run Mimikatz and switch to ‘Minidump’ mode to parse the file as follows.
After this, we can run Mimikatz commands as usual.
Dumping secrets from the registry
We can dump secrets from the registry and parse the files “offline” to get a list of system secrets. 🚩
On the target, we run the following:
Then on our attacking box we can dump the secrets with Impacket:
Dumping secrets from a Volume Shadow Copy
We can also create a “Volume Shadow Copy” of the SAM and SYSTEM files (which are always locked on the current system), so we can still copy them over to our local system. An elevated prompt is required for this.
Disable defender
👀🚩
Or leave Defender enabled, and just remove the signatures from it.
Chisel proxying
Jenkins Manual
Just an example on how to set up a Socks proxy to chisel over a compromised host. There are many more things you can do with Chisel!
On attacker machine (Linux or Windows):
On target:
Now we are listening on localhost:8001 on our attacking machine to forward that traffic to target:9001.
Then, open the Socks server. On target:
Jenkins Command Cheat Sheet
On attacking machine:
A proxy is now open on port 1080 of our attacking machine.
Jenkins Cheat Sheet Pdf
Juicy files
There are lots of files that may contain interesting information. Tools like WinPEAS or collections like PowerSploit may help in identifying juicy files (for privesc or post-exploitation).
Below is a list of some files I have encountered to be of relevance. Check files based on the programs and/or services that are installed on the machine.
In addition, don’t forget to enumerate any local databases with sqlcmd or Invoke-SqlCmd!
