- Apache2 Http To Https Redirect
- Apache2 Redirect To Https Ubuntu
- Http To Https Redirect
- Apache2 Redirect Http To Https
Apache’s mod_rewrite makes it easy to require SSL to be used on your site and to gently redirect users who forget to add the https when typing the URL. Using Apache to redirect http to https will make sure that your site (or a part of it) will only be accessed by your customers using SSL. This is better than using SSLRequireSSL because users often forget to type in the https and will be automatically redirected.
Apache2 Http To Https Redirect
The Apache HTTP Server Project is an effort to develop and maintain an open-source HTTP server for modern operating systems including UNIX and Windows. The goal of this project is to provide a secure, efficient and extensible server that provides HTTP services in sync with the current HTTP standards.
Before you can set up an Apache redirect from http to https, you will need to do the following:
Mar 16, 2017 Configuring Apache for https on CentOS isn't difficult, but there are a few steps. Let's walk through the process, so you can start serving your pages up to your clients/customers more confidently. Whereas HTTPS is the secure version of HTTP, where the ‘S‘ at the end stands for ‘Secure‘. Using HTTPS, all data between your browser and the web server are encrypted thus secure. This tutorial will show you how to redirect HTTP to HTTPS on Apache HTTP server in Linux. Enabling support for HTTP2 on your website and webserver is a very easy process. It shouldn’t take more than a few minutes and cause almost no down-time. The process to configure your Apache web server to support HTTP2 is simple. During this process we will be adding repositories to. I think last time this happened to me it may have been something weird like NameVirtualHost.:80/NameVirtualHost.:443 and/or Listen 80/Listen 443 were somewhere other than ports.conf for apache2. Here is what I have in VirtualHost to redirect to https for all pages except for press (had a video that couldn't be served https so had to redirect back to http otherwise people would get ugly.
- Make sure your SSL certificate is successfully installed so you can access https://www.yoursite.com (for more information see our Apache SSL Installation instructions)
- Make sure mod_rewrite is enabled in Apache
Now you just need to edit your httpd.conf file or the file where your virtual host is specified and add these lines to redirect http to https:
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule (.*) https://%{SERVER_NAME}/$1 [R,L]
In many cases, you can also just add those lines to a file named .htaccess in the folder that you want to redirect http to https.
Now, when a visitor types http://www.yoursite.com/mypage.htm the server will automatically redirect http to https so that they go to https://www.yoursite.com/mypage.htm
Note: You can also redirect a single page from http to http in Apache by using this in your configuration file or .htaccess file:
RewriteEngine On
RewriteRule ^apache-redirect-http-to-https.html$ https://www.yoursite.com/apache-redirect-http-to-https.html [R=301,L]
Originally posted on Sat Feb 20, 2010
By Shayne Boyer
Using this guide, learn how to set up Apache as a reverse proxy server on CentOS 7 to redirect HTTP traffic to an ASP.NET Core web app running on Kestrel server. The mod_proxy extension and related modules create the server's reverse proxy.
Prerequisites
- Server running CentOS 7 with a standard user account with sudo privilege.
- Install the .NET Core runtime on the server.
- Visit the Download .NET Core page.
- Select the latest non-preview .NET Core version.
- Download the latest non-preview runtime in the table under Run apps - Runtime.
- Select the Linux Package manager instructions link and follow the CentOS instructions.
- An existing ASP.NET Core app.
At any point in the future after upgrading the shared framework, restart the ASP.NET Core apps hosted by the server.
Publish and copy over the app
Configure the app for a framework-dependent deployment.
If the app is run locally and isn't configured to make secure connections (HTTPS), adopt either of the following approaches:
- Configure the app to handle secure local connections. For more information, see the HTTPS configuration section.
- Remove
https://localhost:5001(if present) from theapplicationUrlproperty in the Properties/launchSettings.json file.
Run dotnet publish from the development environment to package an app into a directory (for example, bin/Release/<target_framework_moniker>/publish) that can run on the server:
The app can also be published as a self-contained deployment if you prefer not to maintain the .NET Core runtime on the server.
Copy the ASP.NET Core app to the server using a tool that integrates into the organization's workflow (for example, SCP, SFTP). It's common to locate web apps under the var directory (for example, var/www/helloapp).
Note
Under a production deployment scenario, a continuous integration workflow does the work of publishing the app and copying the assets to the server.
Configure a proxy server
A reverse proxy is a common setup for serving dynamic web apps. The reverse proxy terminates the HTTP request and forwards it to the ASP.NET app.
A proxy server forwards client requests to another server instead of fulfilling requests itself. A reverse proxy forwards to a fixed destination, typically on behalf of arbitrary clients. In this guide, Apache is configured as the reverse proxy running on the same server that Kestrel is serving the ASP.NET Core app.
Because requests are forwarded by reverse proxy, use the Forwarded Headers Middleware from the Microsoft.AspNetCore.HttpOverrides package. The middleware updates the Request.Scheme, using the X-Forwarded-Proto header, so that redirect URIs and other security policies work correctly.

Any component that depends on the scheme, such as authentication, link generation, redirects, and geolocation, must be placed after invoking the Forwarded Headers Middleware.
Forwarded Headers Middleware should run before other middleware. This ordering ensures that the middleware relying on forwarded headers information can consume the header values for processing. To run Forwarded Headers Middleware after diagnostics and error handling middleware, see Forwarded Headers Middleware order.
Invoke the UseForwardedHeaders method at the top of Startup.Configure before calling other middleware. Configure the middleware to forward the X-Forwarded-For and X-Forwarded-Proto headers:
If no ForwardedHeadersOptions are specified to the middleware, the default headers to forward are None.
Proxies running on loopback addresses (127.0.0.0/8, [::1]), including the standard localhost address (127.0.0.1), are trusted by default. If other trusted proxies or networks within the organization handle requests between the Internet and the web server, add them to the list of KnownProxies or KnownNetworks with ForwardedHeadersOptions. The following example adds a trusted proxy server at IP address 10.0.0.100 to the Forwarded Headers Middleware KnownProxies in Startup.ConfigureServices:
For more information, see Configure ASP.NET Core to work with proxy servers and load balancers.
Install Apache
Update CentOS packages to their latest stable versions:
Install the Apache web server on CentOS with a single yum command:
Sample output after running the command:
Note
In this example, the output reflects httpd.86_64 since the CentOS 7 version is 64 bit. To verify where Apache is installed, run whereis httpd from a command prompt.
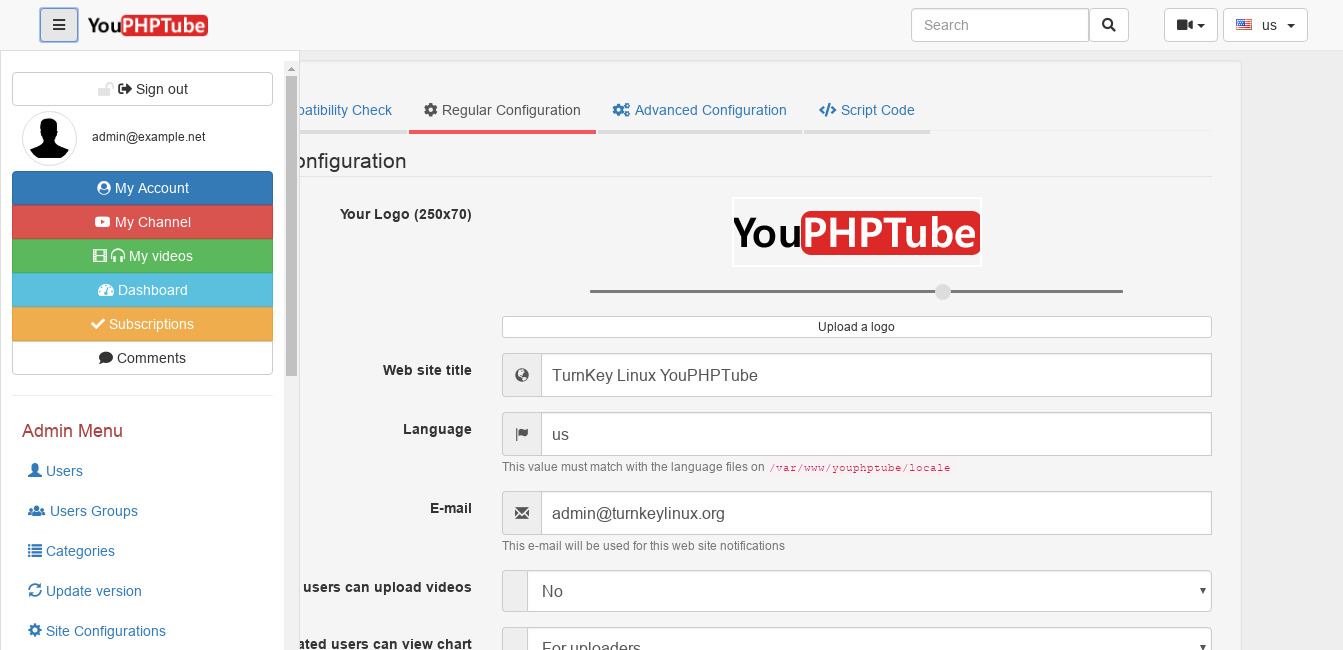
Configure Apache
Configuration files for Apache are located within the /etc/httpd/conf.d/ directory. Any file with the .conf extension is processed in alphabetical order in addition to the module configuration files in /etc/httpd/conf.modules.d/, which contains any configuration files necessary to load modules.
Create a configuration file, named helloapp.conf, for the app:
The VirtualHost block can appear multiple times, in one or more files on a server. In the preceding configuration file, Apache accepts public traffic on port 80. The domain www.example.com is being served, and the *.example.com alias resolves to the same website. For more information, see Name-based virtual host support. Requests are proxied at the root to port 5000 of the server at 127.0.0.1. For bi-directional communication, ProxyPass and ProxyPassReverse are required. To change Kestrel's IP/port, see Kestrel: Endpoint configuration.
The VirtualHost block can appear multiple times, in one or more files on a server. In the preceding configuration file, Apache accepts public traffic on port 80. The domain www.example.com is being served, and the *.example.com alias resolves to the same website. For more information, see Name-based virtual host support. Requests are proxied at the root to port 5000 of the server at 127.0.0.1. For bi-directional communication, ProxyPass and ProxyPassReverse are required. To change Kestrel's IP/port, see Kestrel: Endpoint configuration.
Warning
Failure to specify a proper ServerName directive in the VirtualHost block exposes your app to security vulnerabilities. Subdomain wildcard binding (for example, *.example.com) doesn't pose this security risk if you control the entire parent domain (as opposed to *.com, which is vulnerable). For more information, see rfc7230 section-5.4.
Logging can be configured per VirtualHost using ErrorLog and CustomLog directives. ErrorLog is the location where the server logs errors, and CustomLog sets the filename and format of log file. In this case, this is where request information is logged. There's one line for each request.
Save the file and test the configuration. If everything passes, the response should be Syntax [OK].
Restart Apache:
Monitor the app
Apache is now set up to forward requests made to http://localhost:80 to the ASP.NET Core app running on Kestrel at http://127.0.0.1:5000. However, Apache isn't set up to manage the Kestrel process. Use systemd and create a service file to start and monitor the underlying web app. systemd is an init system that provides many powerful features for starting, stopping, and managing processes.
Create the service file
Create the service definition file:
An example service file for the app:
In the preceding example, the user that manages the service is specified by the User option. The user (apache) must exist and have proper ownership of the app's files.
Use TimeoutStopSec to configure the duration of time to wait for the app to shut down after it receives the initial interrupt signal. If the app doesn't shut down in this period, SIGKILL is issued to terminate the app. Provide the value as unitless seconds (for example, 150), a time span value (for example, 2min 30s), or infinity to disable the timeout. TimeoutStopSec defaults to the value of DefaultTimeoutStopSec in the manager configuration file (systemd-system.conf, system.conf.d, systemd-user.conf, user.conf.d). The default timeout for most distributions is 90 seconds.
Some values (for example, SQL connection strings) must be escaped for the configuration providers to read the environment variables. Use the following command to generate a properly escaped value for use in the configuration file:
Colon (:) separators aren't supported in environment variable names. Use a double underscore (__) in place of a colon. The Environment Variables configuration provider converts double-underscores into colons when environment variables are read into configuration. In the following example, the connection string key ConnectionStrings:DefaultConnection is set into the service definition file as ConnectionStrings__DefaultConnection:
Colon (:) separators aren't supported in environment variable names. Use a double underscore (__) in place of a colon. The Environment Variables configuration provider converts double-underscores into colons when environment variables are read into configuration. In the following example, the connection string key ConnectionStrings:DefaultConnection is set into the service definition file as ConnectionStrings__DefaultConnection:
Save the file and enable the service:
Start the service and verify that it's running:
With the reverse proxy configured and Kestrel managed through systemd, the web app is fully configured and can be accessed from a browser on the local machine at http://localhost. Inspecting the response headers, the Server header indicates that the ASP.NET Core app is served by Kestrel:
View logs
Since the web app using Kestrel is managed using systemd, events and processes are logged to a centralized journal. However, this journal includes entries for all of the services and processes managed by systemd. To view the kestrel-helloapp.service-specific items, use the following command:
For time filtering, specify time options with the command. For example, use --since today to filter for the current day or --until 1 hour ago to see the previous hour's entries. For more information, see the man page for journalctl.
Data protection
Apache2 Redirect To Https Ubuntu
The ASP.NET Core Data Protection stack is used by several ASP.NET Core middlewares, including authentication middleware (for example, cookie middleware) and cross-site request forgery (CSRF) protections. Even if Data Protection APIs aren't called by user code, data protection should be configured to create a persistent cryptographic key store. If data protection isn't configured, the keys are held in memory and discarded when the app restarts.
If the key ring is stored in memory when the app restarts:
- All cookie-based authentication tokens are invalidated.
- Users are required to sign in again on their next request.
- Any data protected with the key ring can no longer be decrypted. This may include CSRF tokens and ASP.NET Core MVC TempData cookies.
To configure data protection to persist and encrypt the key ring, see:
Secure the app
Http To Https Redirect
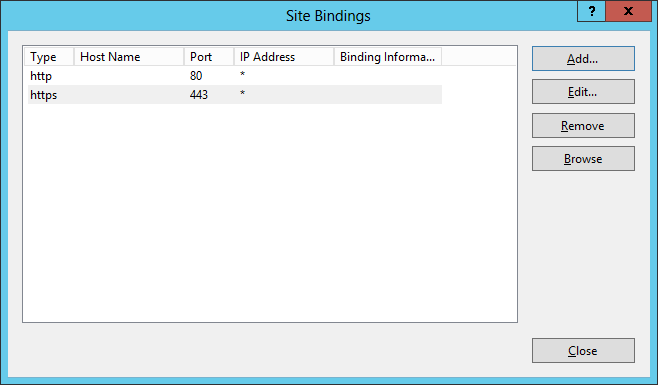
Configure firewall
Firewalld is a dynamic daemon to manage the firewall with support for network zones. Ports and packet filtering can still be managed by iptables. Firewalld should be installed by default. yum can be used to install the package or verify it's installed.
Use firewalld to open only the ports needed for the app. In this case, ports 80 and 443 are used. The following commands permanently set ports 80 and 443 to open:
Reload the firewall settings. Check the available services and ports in the default zone. Options are available by inspecting firewall-cmd -h.
HTTPS configuration
Apache2 Redirect Http To Https
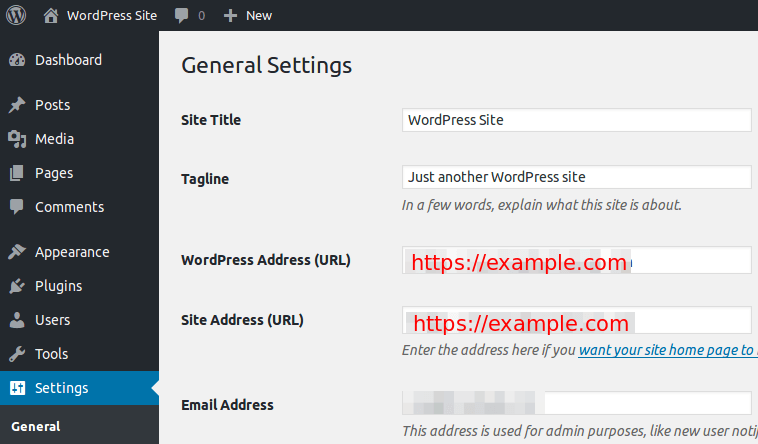
Sims 4 mods pc free. Configure the app for secure (HTTPS) local connections
The dotnet run command uses the app's Properties/launchSettings.json file, which configures the app to listen on the URLs provided by the applicationUrl property (for example, https://localhost:5001;http://localhost:5000).
Configure the app to use a certificate in development for the dotnet run command or development environment (F5 or Ctrl+F5 in Visual Studio Code) using one of the following approaches:
- Replace the default certificate from configuration (Recommended)
- Replace the default certificate from configuration (Recommended)
Configure the reverse proxy for secure (HTTPS) client connections
Warning
The security configuration in this section is a general configuration to be used as a starting point for further customization. 1873 springfield trapdoor serial numbers. We're unable to provide support for third-party tooling, servers, and operating systems. Use the configuration in this section at your own risk. For more information, access the following resources:
- Apache SSL/TLS Encryption (Apache documentation)
To configure Apache for HTTPS, the mod_ssl module is used. When the httpd module was installed, the mod_ssl module was also installed. If it wasn't installed, use yum to add it to the configuration.
To enforce HTTPS, install the mod_rewrite module to enable URL rewriting:
Modify the helloapp.conf file to enable secure communication on port 443.
The following example doesn't configure the server to redirect insecure requests. We recommend using HTTPS Redirection Middleware. For more information, see Enforce HTTPS in ASP.NET Core.
Note
For development environments where the server configuration handles secure redirection instead of HTTPS Redirection Middleware, we recommend using temporary redirects (302) rather than permanent redirects (301). Link caching can cause unstable behavior in development environments.
Adding a Strict-Transport-Security (HSTS) header ensures all subsequent requests made by the client are over HTTPS. For guidance on setting the Strict-Transport-Security header, see Enforce HTTPS in ASP.NET Core.
Note
This example is using a locally-generated certificate. SSLCertificateFile should be the primary certificate file for the domain name. SSLCertificateKeyFile should be the key file generated when CSR is created. SSLCertificateChainFile should be the intermediate certificate file (if any) that was supplied by the certificate authority.
Apache HTTP Server version 2.4.43 or newer is required in order to operate a TLS 1.3 web server with OpenSSL 1.1.1.
Note
The preceding example disables Online Certificate Status Protocol (OCSP) Stapling. For more information and guidance on enabling OCSP, see OCSP Stapling (Apache documentation).
Save the file and test the configuration:
Restart Apache:
Additional Apache suggestions
Restart apps with shared framework updates
After upgrading the shared framework on the server, restart the ASP.NET Core apps hosted by the server.
Additional headers
To secure against malicious attacks, there are a few headers that should either be modified or added. Ensure that the mod_headers module is installed:
Secure Apache from clickjacking attacks
Clickjacking, also known as a UI redress attack, is a malicious attack where a website visitor is tricked into clicking a link or button on a different page than they're currently visiting. Use X-FRAME-OPTIONS to secure the site.
To mitigate clickjacking attacks:
Edit the httpd.conf file:
Add the line
Header append X-FRAME-OPTIONS 'SAMEORIGIN'.Save the file.
Restart Apache.
MIME-type sniffing
The X-Content-Type-Options header prevents Internet Explorer from MIME-sniffing (determining a file's Content-Type from the file's content). If the server sets the Content-Type header to text/html with the nosniff option set, Internet Explorer renders the content as text/html regardless of the file's content.
Edit the httpd.conf file:
Add the line Header set X-Content-Type-Options 'nosniff'. Save the file. Restart Apache.
Load Balancing
This example shows how to setup and configure Apache on CentOS 7 and Kestrel on the same instance machine. To not have a single point of failure; using mod_proxy_balancer and modifying the VirtualHost would allow for managing multiple instances of the web apps behind the Apache proxy server.
In the configuration file shown below, an additional instance of the helloapp is set up to run on port 5001. The Proxy section is set with a balancer configuration with two members to load balance byrequests.
Rate Limits
Using mod_ratelimit, which is included in the httpd module, the bandwidth of clients can be limited:
The example file limits bandwidth as 600 KB/sec under the root location:
Long request header fields
Proxy server default settings typically limit request header fields to 8,190 bytes. An app may require fields longer than the default (for example, apps that use Azure Active Directory). If longer fields are required, the proxy server's LimitRequestFieldSize directive requires adjustment. The value to apply depends on the scenario. For more information, see your server's documentation.
Warning
Don't increase the default value of LimitRequestFieldSize unless necessary. Increasing the value increases the risk of buffer overrun (overflow) and Denial of Service (DoS) attacks by malicious users.
Additional resources
